Last updated on June 3rd, 2021 at 04:36 pm
A New World
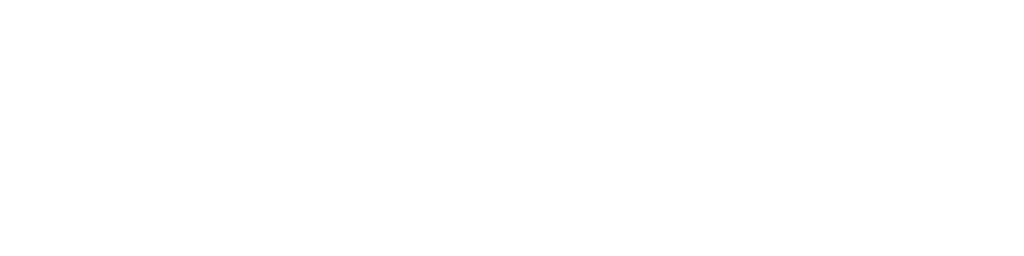
A new world of possibilities was born with the introduction of authentication trees in ForgeRock’s Access Management (AM). Limiting login sequences of the past were replaced with flexible, adaptive, and contextual authentication journeys.
ForgeRock chose the term Intelligent Authentication to capture this new set of capabilities. Besides offering a shiny new browser-based design tool to visually create and maintain authentication trees, Intelligent Authentication also rang in a new era of atomic extensibility.
While ForgeRock’s Identity Platform has always been known for its developer-friendliness, authentication trees took it to the next level: Trees consist of a number nodes, which are connected with each other like in a flow diagram or decision tree. Each node is an atomic entity, taking a single input and providing one or more outputs. Nodes can be implemented in Java, JavaScript, or Groovy.
A public marketplace allows the community to share custom nodes. An extensive network of technology partners provides nodes to integrate with their products and services.
A New Challenge
With the inception of authentication trees, a spike of collaboration between individuals, partners, and customers occurred. At first the sharing happened on a node basis as people would exchange cool custom node jar files with instructions on how to use those nodes. But soon it became apparent that the sharing of atomic pieces of functionality wasn’t quite cutting it. People wanted to share whole journeys, processes, trees.
A New Tool – amtree.sh
A fellow ForgeRock solution architect in the UK, Jon Knight, created the first version of a tool that allowed the easy export and import of trees. I was so excited about the little utility that I forked his repository and extended its functionality to make it even more useful. Shortly thereafter, another fellow solution architect from the Bay Area, Jamie Morgan, added even more capabilities.
The tool is implemented as a shell script, which exports authentication trees from any AM realm to standard output or a file and imports trees into any realm from standard input or a file. The tool automatically includes required decision node scripts for authentication trees (JavaScript and Groovy) and requires curl, jq, and uuidgen to be installed and available on the host where it is to be used. Here are a few ideas and examples for how to use the tool:
Backup/Export
I do a lot of POCs or create little point solutions for customer or prospect use cases or build demos to show off technology partner integrations or our support for the latest open standards. No matter what I do, it often involves authentication trees of various complexity and usually those trees take some time designing and testing and thus are worthy of documentation and preservation and sharing. The first step to achieve any of these things is to extract the trees’ configuration into a reusable format, or simply speaking: backing them up or exporting them.
Before performing an export, It can be helpful to just produce a list of all the authentication trees in a realm. That way we get an idea what’s available and can decide if we want to export individual trees or all the trees in a realm. The tool provides an option to list all trees in a realm. It lists the trees in their natural order (order of creation). To get an alphabetically ordered list, we can pipe the output into the sort shell command.
List Trees
../amtree.sh -h https://am.example.com/openam -u amadmin -p ******** -r /authn -l | sort email push push_reg push_reg_2fa risk select simple smart solid trusona webauthn webauthn_reg webauthn_reg_2fa
Now that we have a list of trees, it is time to think about what it is we want to do. The amtree.sh tool offers us 3 options:
- Export a single tree into a file or to standard out: -e
- Export all trees into individual files: -S
- Export all trees into a single file or to standard out: -E
The main reason to choose one of these options over another is whether your trees are independent (have no dependency on other trees) or not. Authentication trees can reference other trees, which then act like subroutines in a program. These subroutines are called inner trees. Independent trees do not contain inner trees. Dependent trees contain inner trees.
Options 1 and 2 are great for independent trees as they put a single tree into a single file. Those trees can then easily be imported again. Option 2 generates the same output as if running option 1 for every tree in the realm.
Dependent trees require other trees be already available or be imported before the dependent tree is imported or the AM APIs will complain and the tool will not be able to complete the import.
Option 3 is best suited for highly interdependent trees. It puts all the trees of a realm into the same file and on import of that file, the tool will always have all the required dependencies available.
Option 2: Export All Trees To Individual Files
../amtree.sh -h https://am.example.com/openam -u amadmin -p ******** -r /authn -S Export all trees to files Exporting push .......... Exporting simple ............ Exporting trusona .... Exporting risk ........ Exporting smart .......... Exporting webauthn ............. Exporting select ....... Exporting solid ...... Exporting webauthn_reg ............ Exporting webauthn_reg_2fa ............. Exporting email ......... Exporting push_reg .............. Exporting push_reg_2fa ...............
Option 3: Export All Trees To Single File
../amtree.sh -h https://am.example.com/openam -u amadmin -p ******** -r /authn -E -f authn_all.json Exporting push .......... Exporting simple ............ Exporting trusona .... Exporting risk ........ Exporting smart .......... Exporting webauthn ............. Exporting select ....... Exporting solid ...... Exporting webauthn_reg ............ Exporting webauthn_reg_2fa ............. Exporting email ......... Exporting push_reg .............. Exporting push_reg_2fa ...............
After running both of those commands, we should find the expected files in our current directory:
ls -1 authn_all.json email.json push.json push_reg.json push_reg_2fa.json risk.json select.json simple.json smart.json solid.json trusona.json webauthn.json webauthn_reg.json webauthn_reg_2fa.json
The second command (option 3) produced the single authn_all.json file as indicated by the -f parameter. The first command (option 2) generated individual files per tree.
Restore/Import
Import is just as simple as export. The tool brings in required scripts and resolves dependencies to inner trees, which means it orders trees on import to satisfy dependencies.
Exports omit secrets of all kind (passwords, API keys, etc.) which may be stored in node configuration properties. Therefore, if we exported a tree whose configuration contains secrets, the imported tree will lack those secrets. If we want to more easily reuse trees (like I do in my demo/lab environments) we can edit the exported tree files and manually insert the secrets. Fields containing secrets are exported as null values. Once we manually add those secrets to our exports, they will import as expected.
{
"origin": "003232731275e50c2770b3de61675fca",
"innernodes": {},
"nodes": {
...
"B56DB408-E26D-4FBA-BF86-339799ED8C45": {
"_id": "B56DB408-E26D-4FBA-BF86-339799ED8C45",
"hostName": "smtp.gmail.com",
"password": null,
"sslOption": "SSL",
"hostPort": 465,
"emailAttribute": "mail",
"smsGatewayImplementationClass": "com.sun.identity.authentication.modules.hotp.DefaultSMSGatewayImpl",
"fromEmailAddress": "vscheuber@gmail.com",
"username": "vscheuber@gmail.com",
"_type": {
"_id": "OneTimePasswordSmtpSenderNode",
"name": "OTP Email Sender",
"collection": true
}
},
...
},
"scripts": {
...
},
"tree": {
"_id": "email",
"nodes": {
...
"B56DB408-E26D-4FBA-BF86-339799ED8C45": {
"displayName": "Email OTP",
"nodeType": "OneTimePasswordSmtpSenderNode",
"connections": {
"outcome": "08211FF9-9F09-4688-B7F1-5BCEB3984624"
}
},
...
},
"entryNodeId": "DF68B2B8-0F10-4FF3-9F2C-622DA16BA4B7"
}
}
The Json code snippet above shows excerpts from the email tree. One of the nodes is responsible for sending a one-time password (OTP) via email to the user, thus needing SMTP gateway configuration. The export does not include the value of the password property in the node configuration. To make this export file re-usable, we could replace null with the actual password. Depending on the type of secret this might be acceptable or not.
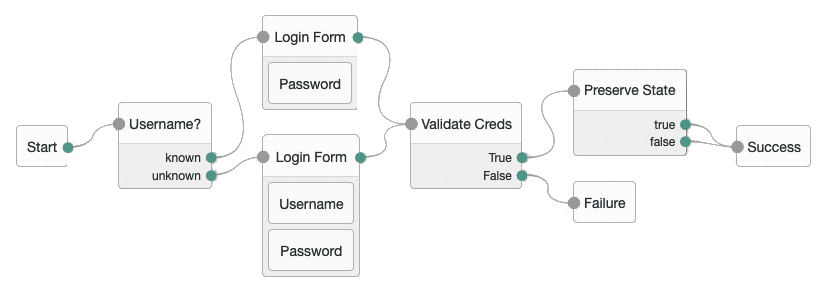
Importing individual trees requires us to make sure all the dependencies are met. Amtree.sh provides a nice option, -d, to describe a tree export file. That will tell us if a tree has any dependencies we need to meet before we can import that single tree. Let’s take the select tree as an example. The select tree offers the user a choice, which 2nd factor they want to use to login. Each choice then evaluates another tree, which implements the chosen method:
Running amtree.sh against the exported select.json file gives us a good overview of what the select tree is made of, which node types it uses, which scripts (if any) it references, and what other trees (inner trees) it depends on:
../amtree.sh -d -f select.json Tree: select ============ Nodes: ----- - ChoiceCollectorNode - InnerTreeEvaluatorNode Scripts: ------- None Dependencies: ------------ - email - push - trusona - webauthn
From the output of the -d option we can derive useful information:
- Which nodes will we need to have installed in our AM instance? ChoiceCollectorNode and InnerTreeEvaluatorNode.
- Which scripts will the tree export file install in our AM instance? None.
- Which trees does this tree depend on? The requiring of the InnerTreeEvaluatorNode already gave away that there will be dependencies. This list simply breaks them down: email, push, trusona, and webauthn.
Ignoring the dependencies we can try to import the file into an empty realm and see what amtree.sh will tell us:
../amtree.sh -h https://am.example.com/openam -u amadmin -p ******** -r /empty -i select -f select.json
Importing select…Error importing node InnerTreeEvaluatorNode (D21C798F-D4E9-400A-A038-0E1A883348EB): {"code":400,"reason":"Bad Request","message":"Data validation failed for the attribute, Tree Name"}
{
"_id": "D21C798F-D4E9-400A-A038-0E1A883348EB",
"tree": "email",
"_type": {
"_id": "InnerTreeEvaluatorNode",
"name": "Inner Tree Evaluator",
"collection": true
}
}
The error message confirms that dependencies are not met. This leaves us with 3 options:
- Instruct amtree.sh to import the four dependencies using the -i option before trying to import select.json. Of course that bears the risk that any or all of the 4 inner trees have dependencies of their own.
- Instruct amtree.sh to import the authn_all.json using the -I option. The tool will bring in all the trees in the right order but there is no easy way to avoid any of the many trees in the file to be imported.
- Instruct amtree.sh import all the .json files in the current directory using the -s option. The tool will bring in all the trees in the right order. Any trees we don’t want to import, we can move into a sub folder and amtree.sh will ignore them.
Let’s see how option 3 will work out. To avoid errors, we need to move the authn_all.json file containing all the trees into a sub folder, ignore in my case. Then we are good to go:
../amtree.sh -h https://am.example.com/openam -u amadmin -p ******** -r /empty -s Import all trees in the current directory Determining installation order.............................................. Importing email......... Importing push_reg.............. Importing push_reg_2fa............... Importing simple............ Importing trusona.... Importing webauthn............. Importing webauthn_reg............ Importing webauthn_reg_2fa............. Importing push.......... Importing risk........ Importing select....... Importing smart.......... Importing solid......
No errors reported this time. You can see the tools spent quite some cycles determining the proper import order (the more dots, the more cycles). We would have likely run into nested dependencies had we tried option 1 and manually imported the four known dependencies.
A word of caution: Imports overwrite trees of the same name without any warning. Be mindful of that fact when importing into a realm with existing trees.
Migrate/Copy
Amtree.sh supports stdin and stdout for input and output. That allows us to pipe the output of an export command (-e or -E) to an import command (-i or -I) without storing anything on disk. That’s a pretty slick way to migrate trees from one realm to another in the same AM instance or across instances. The -s and -S options do not support stdin and stdout, thus they won’t work for this scenario.
../amtree.sh -h https://am.example.com/openam -u amadmin -p ******** -r /authn -E | ../amtree.sh -h https://am.example.com/openam -u amadmin -p ******** -r /empty -I Exporting push .......... Exporting simple ............ Exporting trusona .... Exporting risk ........ Exporting smart .......... Exporting webauthn ............. Exporting select ....... Exporting solid ...... Exporting webauthn_reg ............ Exporting webauthn_reg_2fa ............. Exporting email ......... Exporting push_reg .............. Exporting push_reg_2fa ............... Determining installation order............................. Importing email......... Importing push.......... Importing push_reg.............. Importing push_reg_2fa............... Importing risk........ Importing select....... Importing simple............ Importing smart.......... Importing solid...... Importing trusona.... Importing webauthn............. Importing webauthn_reg............ Importing webauthn_reg_2fa.............
The above command copies all the trees in a realm to another realm. Nothing is ever exported to disk.
Prune
Trees consist of different configuration artifacts in the AM configuration store. When managing trees through the AM REST APIs, it is easy to forget to remove unused artifacts. Even when using the AM Admin UI, dead configuration is left behind every time a tree is deleted. The UI doesn’t give an admin any options to remove those dead artifacts nor is there a way really to even see them. Over time, they will grow to uncomfortable size and will clutter the results of API calls.
Amtree.sh prunes those orphaned configuration artifacts when the -P parameter is supplied. I regularly delete all the default trees in a new realm, which leaves me with 33 orphaned configuration artifacts right out of the gate. To be clear: Those orphaned configuration artifacts don’t cause any harm. It’s a desire for tidiness that makes me want them gone.
./amtree.sh -h https://am.example.com/openam -u amadmin -p ******** -r /authn -P Analyzing authentication nodes configuration artifacts… Total: 118 Orphaned: 20 Do you want to prune (permanently delete) all the orphaned node instances? (N/y): y Pruning.................... Done.
Wrap-Up & Resources
Amtree.sh is a big improvement for the handling and management of authentication trees in the ForgeRock Identity Platform. It is hardly the final solution, though. The implementation as a shell script is limiting both the supported platforms and functionality. My fingers are itching to re-write it in a better suited language. Now there’s a goal for 2020!
If you want to explore the examples in this post, here are all the resources I used:
- amtree.sh – I am using my own fork, which currently seems to be the most functional.
- authn.zip – This archive includes all the individual tree export files from the -S export and, in the ignore sub folder, the authn_all.json, which contains all the trees in a single file generated with -E.
- Nodes not included in AM 6.5:
- Push Reg Node – Get it from the marketplace or github. I compiled and used this pushreg-node-6.5.0.1.jar.
- GeoLocation Node – Get it from the marketplace or github. I compiled and used this GeoLocationNode-6.5.0.1-SNAPSHOT.jar.
- IP Address Decision Node – Get it from the marketplace or github. I compiled and used this ip-address-decision-auth-tree-node-6.5.0.jar.
- Have I Been Pwned Password Node – I used this haveibeenpwnedpassword-node-6.0.0.jar, which I got from a colleague. I can’t find it in github or on the marketplace. I will look into that. But for all I know, the jar is good to use.
- Search For User Node – Get it from the marketplace or github. I compiled and used this search-for-user-node-6.5.0.jar.
- Trusona Decision Node – Get it from the marketplace or github. I compiled and used this trusona-forgerock-node-2.0.2-all.jar.
Awesome. This blog looks to be a valuable addition to online resources about the ForgeRock platform and other identity-related matters – now bookmarked!